OAuth Grant types
Introduction
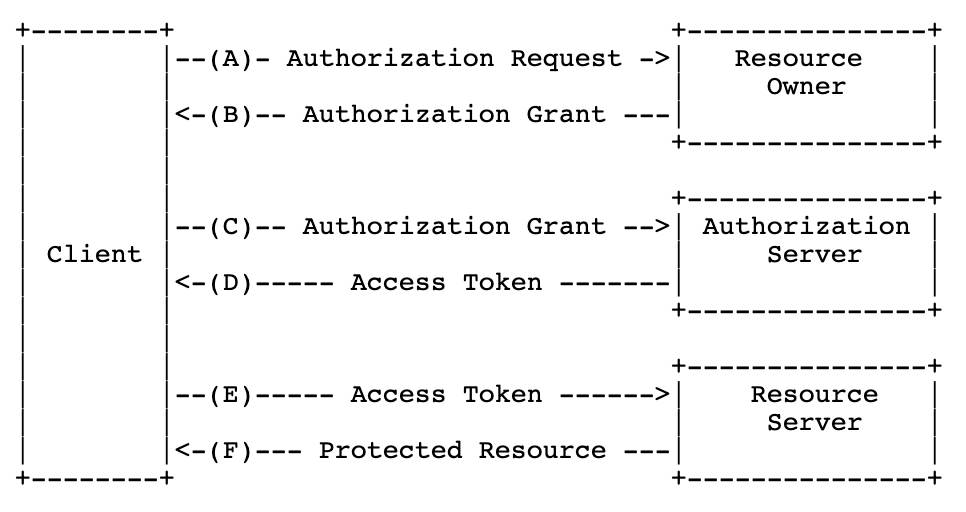
The OAuth 2.0 Authorization Framework specifies a protocol for interaction between resource owners (users), clients (applications), authorization servers and resource servers. This protocol is based on the use of Access tokens, as a way for the client to request an end user's protected resources with the end user's approval, without compromising or exposing the end user's credentials.
Accordingly, an authorization grant is a method for which the client can obtain the Access token needed to get the end user's data. The BankID OIDC Provider supports two grant types - the Authorization Code Flow and the Client Credentials Flow - which are used independently or combined in our different products. PAdES and SEID-SDO signing, for example, start out with a client credential flow (where the Access token is used to create and upload the sign order) followed by an authorization code flow (where the Access token is used to download the completed sign order from the resource server).
Authorization Code Flow
In the context of the BankID OIDC provider, the authroization code flow concerns the authentication of end users, followed by authorization of access to other BankID resource servers in form of an Access token. In short;
- The end user authenticates, and is returned to the client via the redirectURL
- The client receives an authorization code from the BankID OIDC provider (B), and uses this in exchange for tokens via the Token endpoint (C/D)
- The ID token identifies the user
- The Access token can be used to access other resource servers (E/F), for example in the context of electronic signing or digital onboarding processes
- The Refresh token can be used to issue new Access tokens
Client Credential Flow
In the context of the BankID OIDC provider, the client credential flow concerns authorization of access to BankID resource servers directly from an OIDC Client, without involving an end-user. In short;
- The client requests an Access token from the BankID OIDC provider (C)
- If the client credentials are valid (see client authentication), the client receives an Access token (D), which can be used to request other resources (E/F)